The CSA Enterprise Architecture (EA) is both a methodology and a set of tools. It is a framework, a comprehensive approach for the architecture of a secure cloud infrastructure and can be used to assess opportunities for improvement, create roadmaps for technology adoption, identify reusable security patterns, and assess various cloud providers and security technology vendors against a common set of capabilities.
To create the CSA Enterprise Architecture, the EA Working Group leveraged four industry standard architecture models: TOGAF, ITIL, SABSA, and Jericho, therefore combining the best of breed architecture paradigms into a comprehensive approach to cloud security. By merging business drivers with security infrastructure, the EA increases the value proposition of cloud services within an enterprise business model. The CSA Enterprise Architecture was adopted by the National Institute of Standards and Technologies in NIST SP 500-299 and NIST SP 500-292.
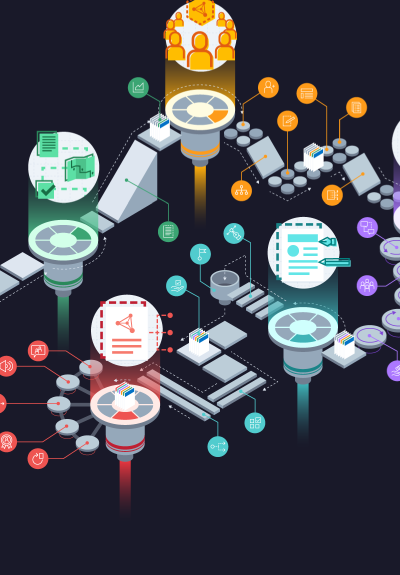
This diagram provides a broad overview and visual representation of the Enterprise Architecture. It is intended as your quick reference guide. For a full explanation of each domain and its components, refer to the Enterprise Architecture v2 Reference Guide.
To learn how the EA maps to CSA’s standard controls set, refer to the Enterprise Architecture v2 to CCM v3.01 Mapping.
Key Takeaways:
- A visualization of CSA’s Enterprise Architecture
- The key components of a secure, identity-aware cloud infrastructure
Download this Resource
 Best For:
Best For:
- Cybersecurity architects
- Cloud engineers
- Cloud security professionals
- Compliance professionals